Youtube
The Bandwidth Killer
to be honest i learn a lot from youtube whether cisco configuration or paloalto or even other things
but during work hour many user using youtube to hear songs, watch a movie trailer which kill the internet bandwidth so i explain earlier how to block facebook using APP-ID
but Youtube APP-ID is little diffrent cause it depend in google-base which will forbid google website too
so URL Category may save the Day
this remind me of Microsoft TMG
So first let create a URL Category
Go to Objects – Custom objects – URL Category – add new
(Youtube)
Add URL (www.youtube.com) Also you can add more (*.youtube.com)

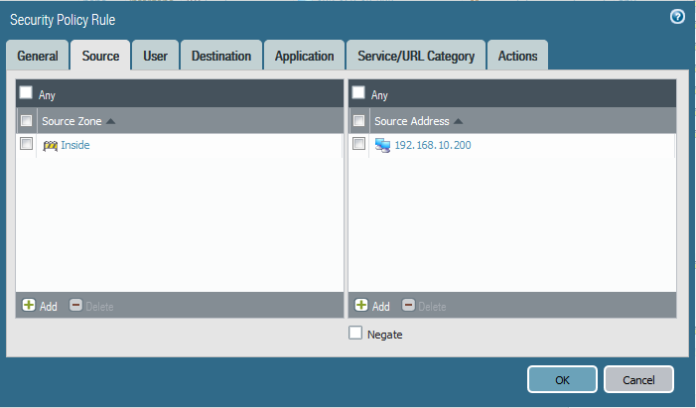
now we create a security policy
Go to Policies – Security – add new (Stop Youtube)

Select the Source Zone (inside) and the Source Address (My Laptop IP Address)
Select the user aysar.mohamed (Me)
Select the Destination as my Outside Interface
Select any in Application tab
well here we go
in Service/URL Category we select the (Youtube) Category that we create earlier
put the Action to deny
now when i try to open Youtube i got the deny messgae ;D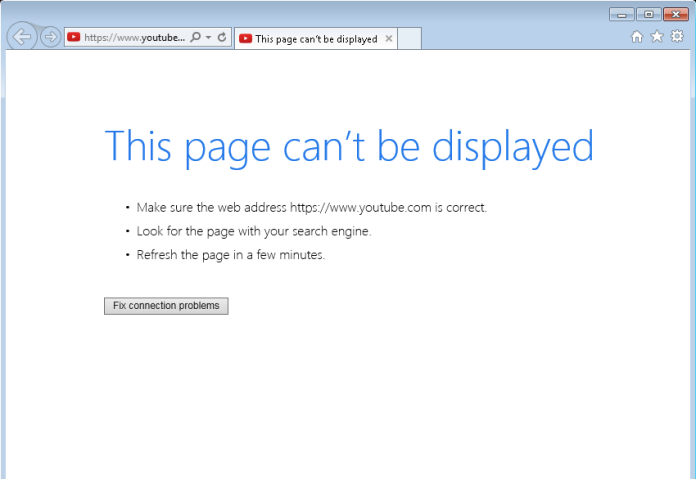
As you can see from the log i got the (Reset-both ) Action in rule of Stop youtube 
;D
This is ugly solution because user does not get notification just 404.
Create URL profile where action for this custom category is block.
Change action in your current policy to “allow”.
Leave URL category in place and add URL blocking profile that you just created.
In this case this policy only applies if user goes to youtube url, traffic gets to HTTP GET and block page is shown to user.
Also you might want to block application quic because Chrome uses quic to communicate with Google services.
There are other things to get better results like also utilizing app-id and applying decryption but this is good for a start.
And if HR does not permit to block youtube then QoS to 100Kbit 🙂
LikeLike
Well I was actually trying to use the feature plus how I did it
But I find your solution is really advanced and I will try it
LikeLike
this didn’t work for me. the rule doesn’t get matched at all.
LikeLike
Hello Maha
i actually implemnt the same solution in over 5 sites and its working perfectly
may i ask did you also add the other option
*.youtube.com
also
*.youtube.*
also in monitoring tab which policy are you matching
if i can understand the full scenario i may solve it
LikeLike
Hi there,
I added those as well but still no luck.
the rule that my traffic is hitting is another one down in the list. I made the block_youtube rule #1.
LikeLike
Hi Mah
in my Previous Article of blocking facebook i add decryption policy so it might cause your traffic is an SSL that why your palo alto cant read it if he cant decrypt it
so try to use the same method and i will also check from my side
LikeLike