Active Directory Integration
In earlier Blog Palo Alto to Internet we configure how to Allow users to go to the Internet. Now Active directory allow me to control who can have an access to internet Per User and also monitor exactly whom watching who and this is the configuration
Let’s start by Microsoft Side
lets start by creating a user in the Active Directory for the mapping integration
go to Tools – Active Directory Users and Computers

Go to the user container and right click New – User
i created a user aysar.mohamed@ccieroot.com
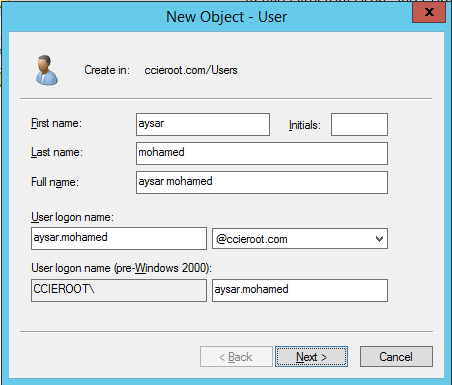
put the password and since this is an integration user no need to change the password and to never expire

Click Finish

go to the user settings

go to the member tab
the user should be Member of :
(Distribute COM User, Event Log Readers, Server Operation)

In Windows 2003, the service account must be given the “Audit and manage security log” user right through a group policy. Making the account a member of the Domain Administrators group provides rights for all operations. The built-in group named “Event Log Readers” is not available in Windows 2003.
Add those Group

Press OK

Second we need to check if the Domain configure to log successful logon
Open Group Policy Management

Then select Domains – ccieroot.com – Default Domain Policy – edit

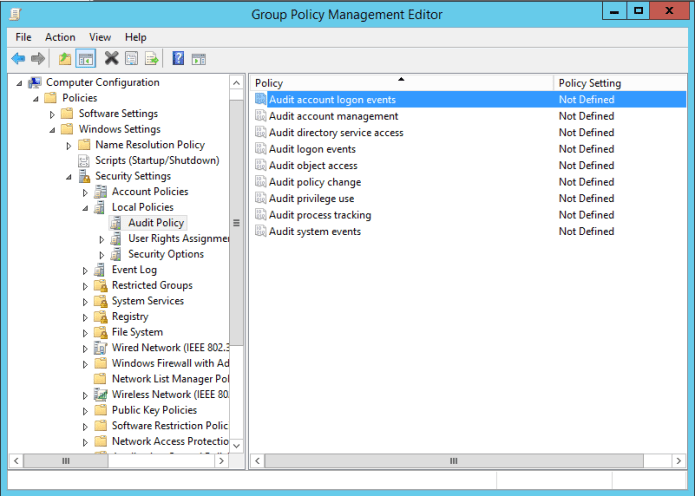
go to Computer Configuration – Windows Settings – Security Settings – Local Policies – Audit Policy
Select Audit Account logon events
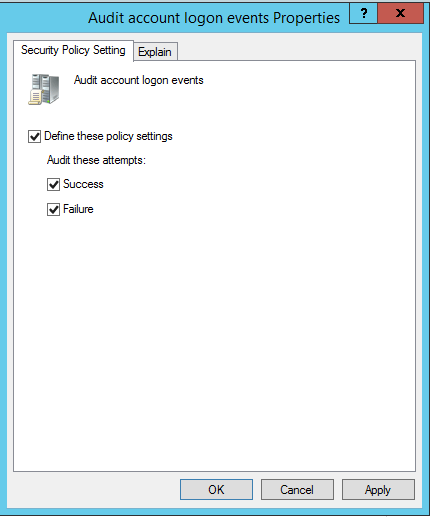
Check box Define these Policy settings
Success & Failure
Now it’s about time to update the policy
Go to cmd and update the policy using the command (gpupdate)
then do the WMI Authentication part as The device uses WMI Authentication and the user must modify the CIMV2 security properties on the AD server that connects to the device.
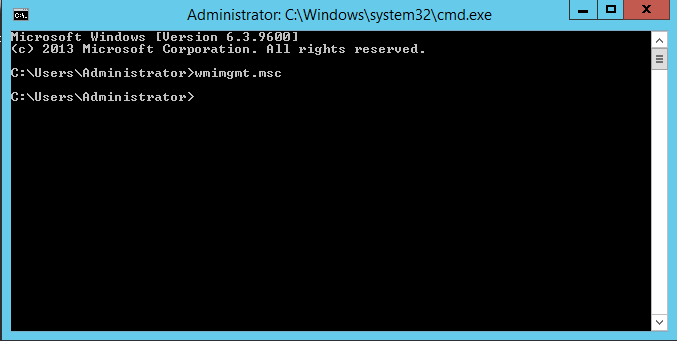
go to cmd and input the command (wmimgmt.msc)
Right Click and select properties

go to Security Tab – Root – CIMV2 and click on Security button

click on Add to add the user (aysar.mohamed) that i created earlier
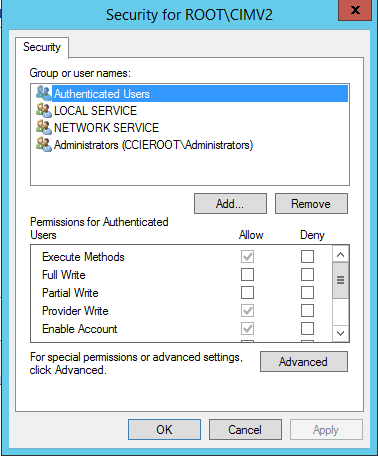

and give him permission:
Enable Account
Remote Enable

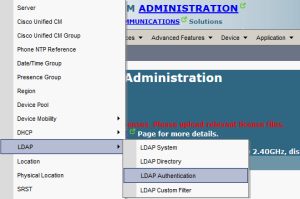
Now The Palo Alto Side
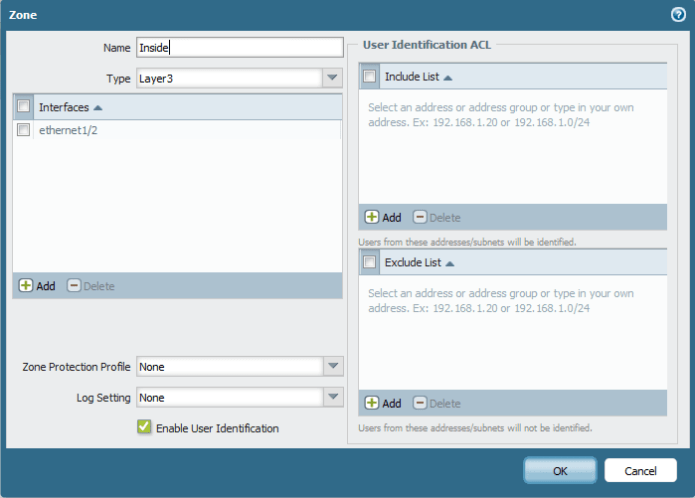
1st check the Internal Zone to have User-ID Enabled
Second make sure the Service route is configure to use the Inside Network for (LDAP, DNS and Kerberos)
go to Device – Setup – Service Feature – Customize

Next Go to Device > User Identification > Palo Alto Network user-ID Agent Setup > Click on settings button on the corner
in WMI Authentication i will use the username and password i created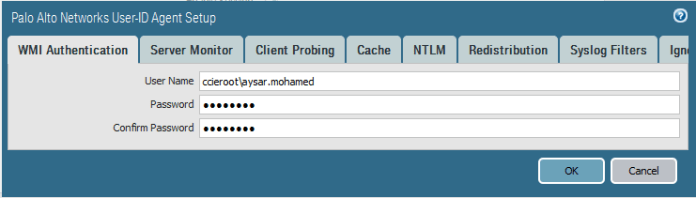
Then Enable the Server Monitoring

Optionally if you enable the NTLM is to discover domain you have to enable DNS configuration under
service – DNS – internal primary dns server
Also Enable the Client Probing and press ok
client probing is useful in huge environment because change will reflect on firewall immediately
every 20 minute

After That i will add my Active directory Under the server Monitoring
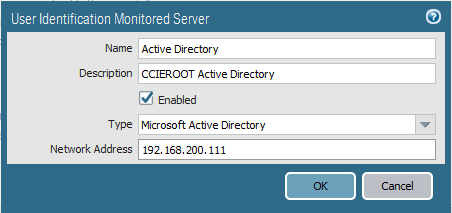
Then the Domain Controllers will show with a status of Connected.
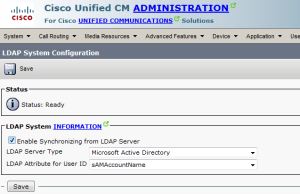
First go to Device – Server Profiles – LDAP – add
Base DN: auto generate
Bind DN : (this account must be a member of the built-in Server Operators group in AD)
Also uncheck the box Require SSL/TLS secured connection

Then we need to create an Authentication Profile
Login Attribute: sAMAccountName
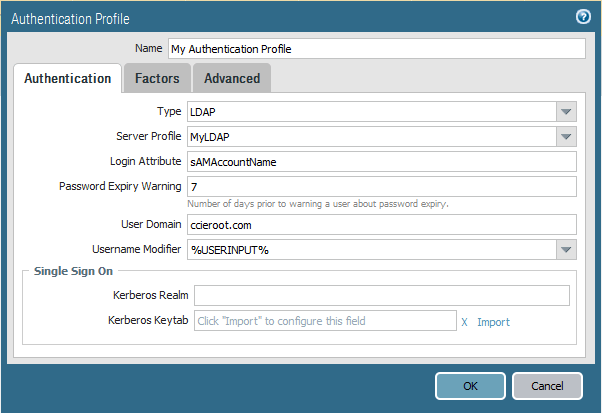
then Select Advanced tab and in the Allow list select to add (All)
Like that we done from Active Directory Integration
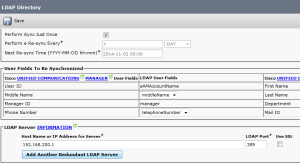
Now we create our group mappings so we can use these Active Directory groups in our security policies.
navigating to the Group Mapping Settings tab – Add new
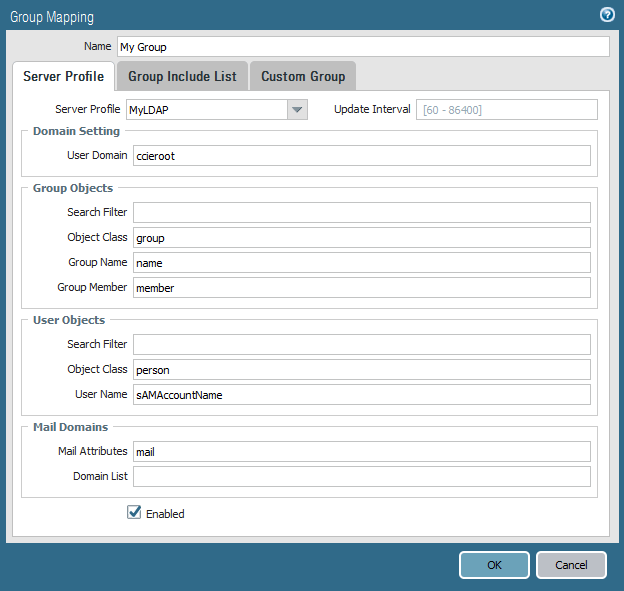
then go to the group include list tab at the top. as long you see the OU in your AD then it mean you can see everything correctly
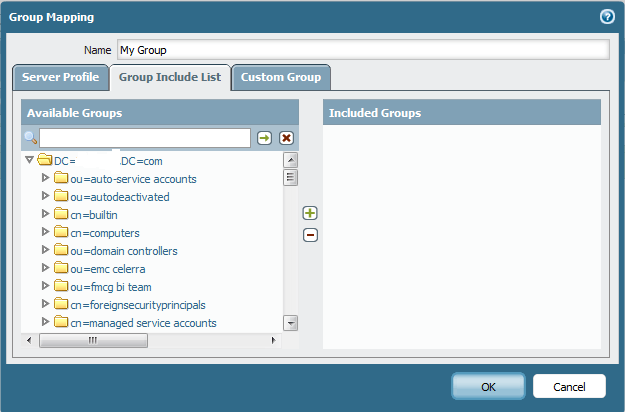
Just for testing i Add the IT Staff

Now on our Internet Rule Select under User tab and Add my user or group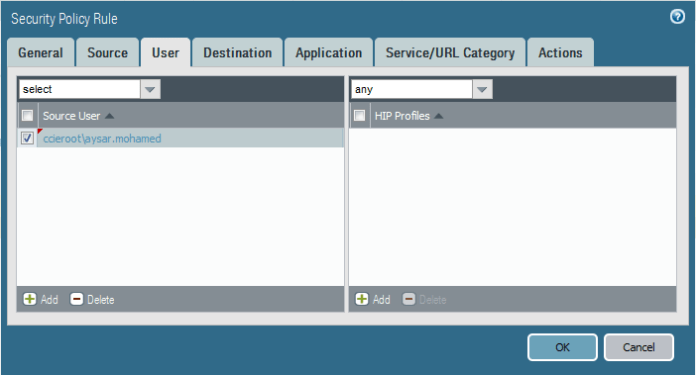
now as you can see under the Monitoring Tab i see my Username when i Access any website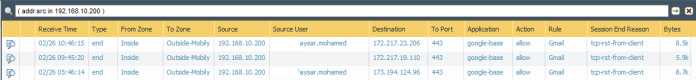
;D
Note:
Because WMI probing trusts data that is reported back from an endpoint, Palo Alto Network recommends that you do not use this method to obtain User-ID mapping information in a high-security network. If you configure the User-ID agent to obtain mapping information by parsing Active Directory (AD) security event logs or syslog messages, or using the XML API, Palo Alto Networks recommends you disable WMI probing.
If you do use WMI probing, do not enable it on external, untrusted interfaces.