OMG one of the best last moment for me in 2018 was last October when me and the Crew attend GITEX the world of technology in Dubai (United Arab of Emirate)

IT’S THE BIGGEST & BOLDEST TECH SHOW IN MENA & SOUTH ASIA
attendees from 120+ countries and global media outlets in unpacking the big conversations and latest solutions around AI, blockchain, robotics, cloud and other mega trends, as GITEX takes you on a multi-sensory experience of Future Urbanism across 21 halls with 4,000 exhibitors across 24 sectors.
and here im going to tell you my new article
So Let me tell you, in my years in network i have never implemented a Site-to-Site VPN and i mean never ever in any product wither Cisco, Juniper or Palo Alto
so i spend reading the Last Couple of days reading and study about it and Thanks to My Mentor Mr.Keith barker from CBT Nugget https://www.cbtnuggets.com/trainers/keith-barker he Got His own way to Make the most Difficult thing Easier than you can imagine.
you can find his Palo Alto video in this Link https://www.cbtnuggets.com/it-training/palo-alto-networks-firewall
So Let’s Start, i have 2 Site
One with Palo Alto VM Machine and the Second Site i have Cisco Router 2811
I put Simple IKE Phase 1 and Phase 2
IKE 1
DH Group: group1
Encryption: aes128
Authentication: sha1
Lifetime: 5 Minute (300 seconds)
IKE 2
IPSEC Protocol: ESP
DH Group: group1
Encryption: aes128
Authentication: sha1
Lifetime: 5 Minute (300 seconds)
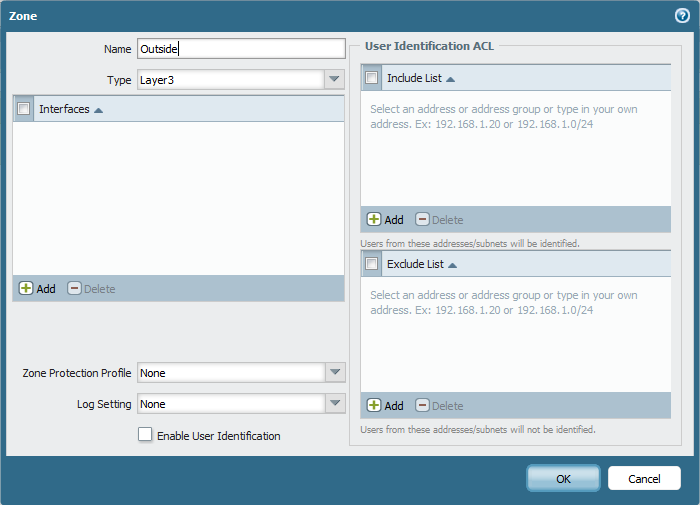
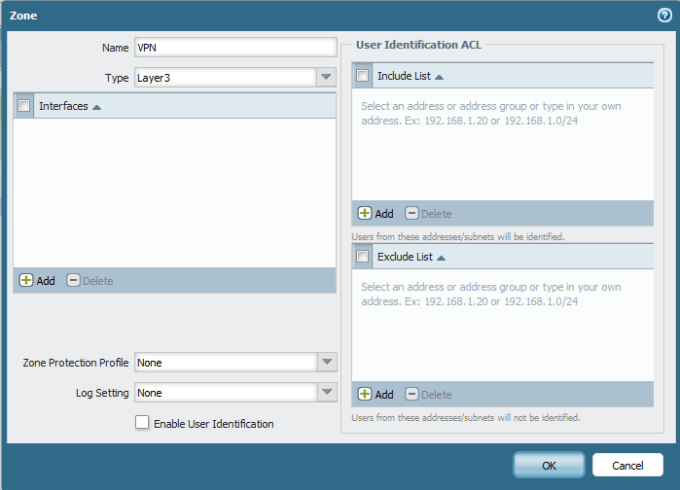
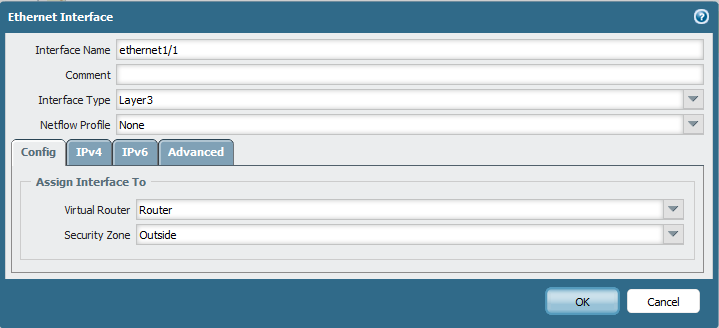
So First Create a VPN Zone Like i Show you in the First Blog
go to Network – Zones – Add new
Then create the tunnel interface
Go to Network – Interface – Select the Tunnel tab – Add new
I Choose number 1 and i have one virtual Router and Select the Zone (VPN)
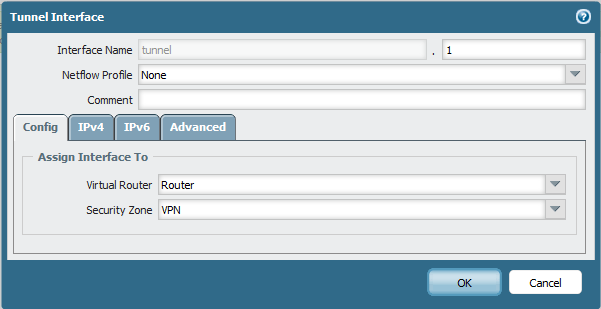
Give the Tunnel an IP Address under the IPV4 tab (10.1.1.40)
Now Lets Create the Phase 1
go to Network – Network profile – IKE Crypto – Add new
i Configure it as my scenario
DH Group: group1
Encryption: aes128
Authentication: sha1
Lifetime: 5 Minute (300 seconds)

After that i create the IKE Gateway
Go to Network – Network profile – IKE Gateways – Add new
Select the WAN interface and Choose static for my Peer since i know the IP Address and Put the Pre-shared Key (ccieroot)
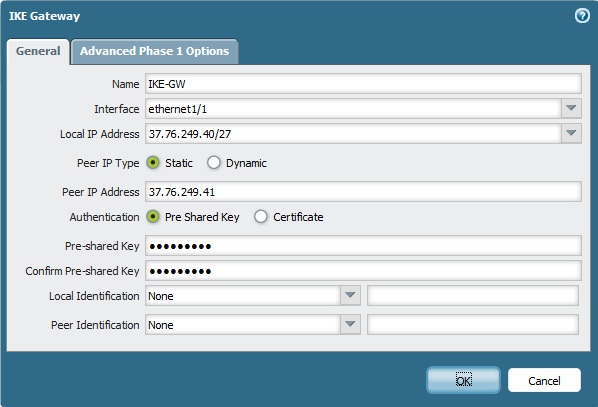
go to Advanced tab to Select the IKE Crypto profile and Choose the IKE Crypto for IKE1 i Created Earlier
Now to IKE2 Configuration
Go to Network – Network profile – IPSec Crypto – Add new
and Same like IKE1 we will follow out Scenario
IPSEC Protocol: ESP
DH Group: group1
Encryption: aes128
Authentication: sha1
Lifetime: 5 Minute (300 seconds)

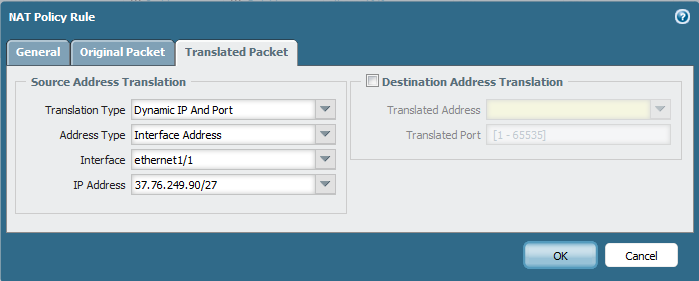
After that i will Configure the IPSec Tunnel
Go to Network – IPSec tunnel – Add new
Select the Tunnel interface, IKE Gateway and IPSec Crypto profile
Now i Create a Static Route to Site 2 LAN
Go to Network – Virtual Router – Select Our Router – Edit – Static Route Tab – Add new
type the Destination of Site2 LAN and Select your Tunnel 1 and Type Site2 Tunnel Interface IP Address as My Next hop

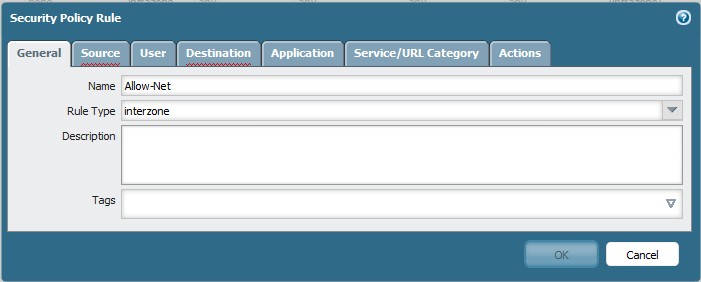
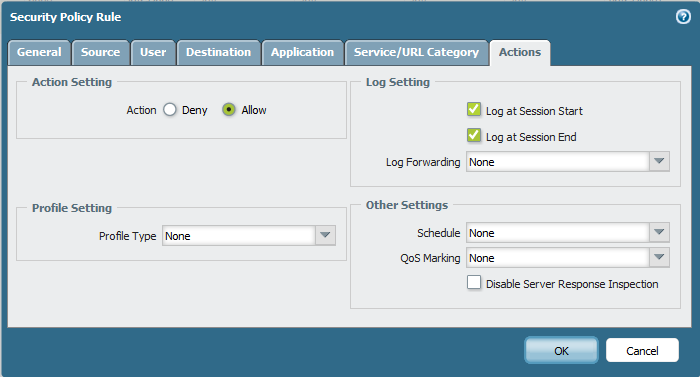
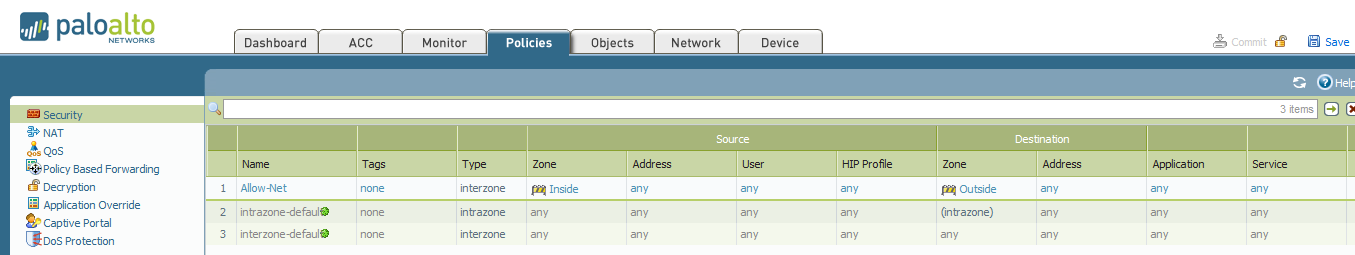
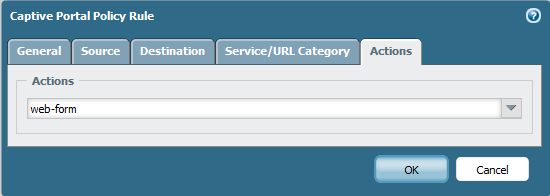
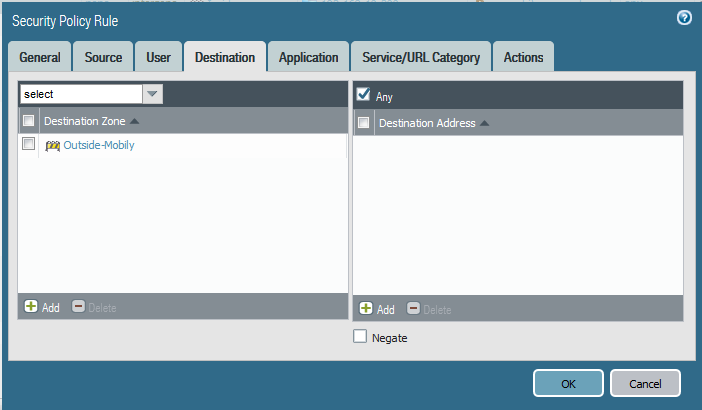
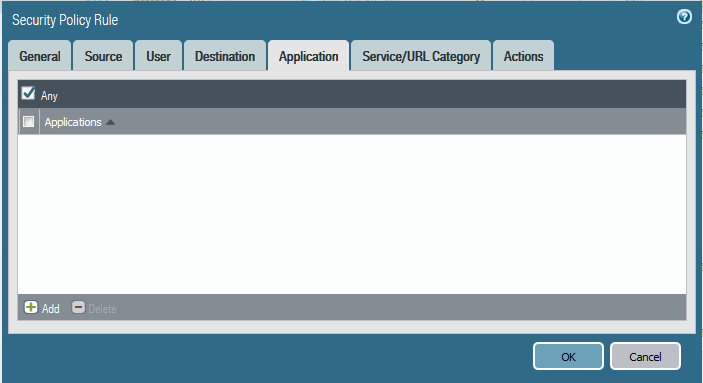
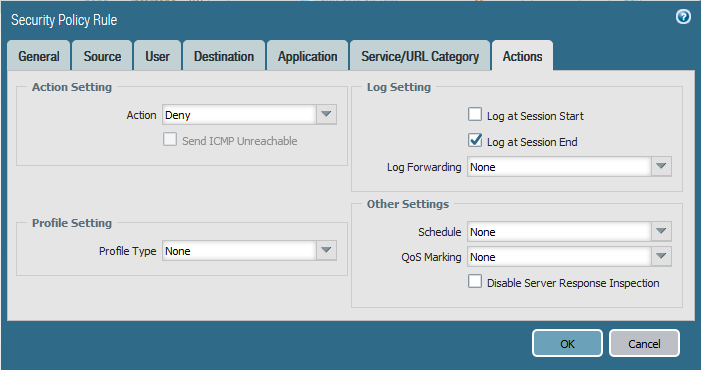
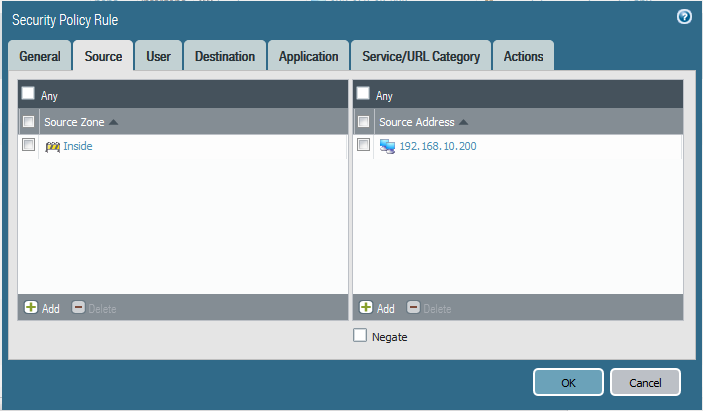
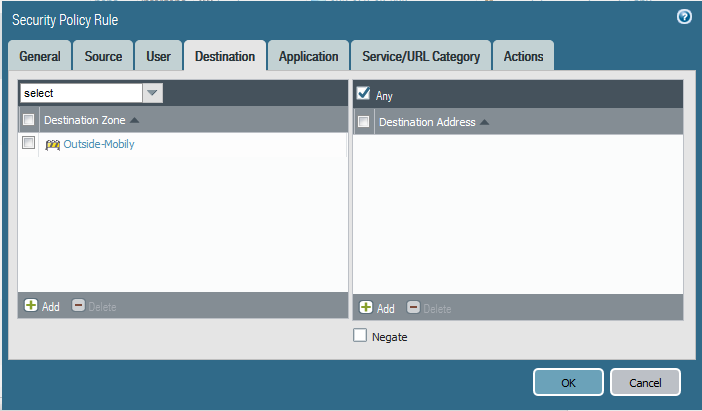
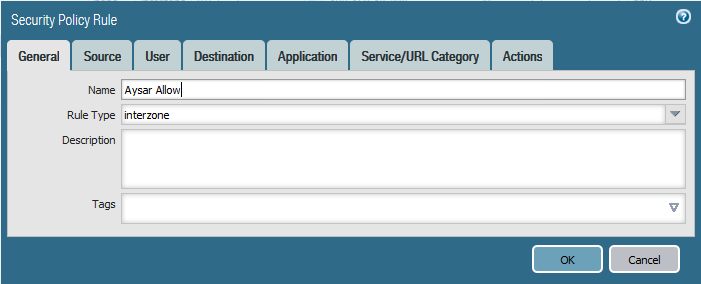
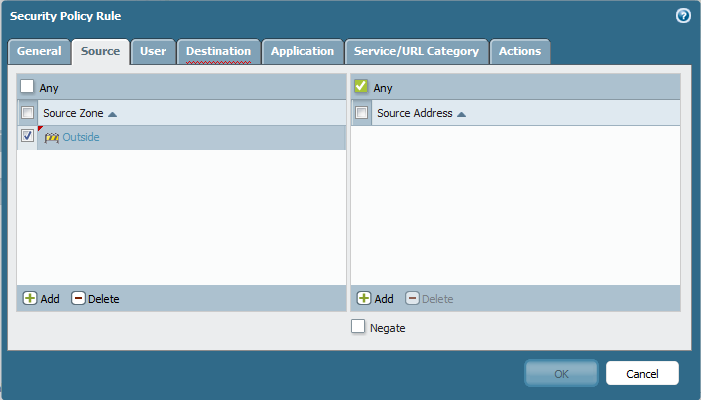
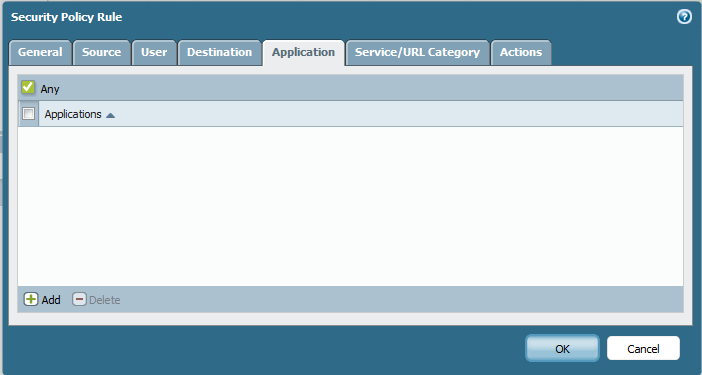
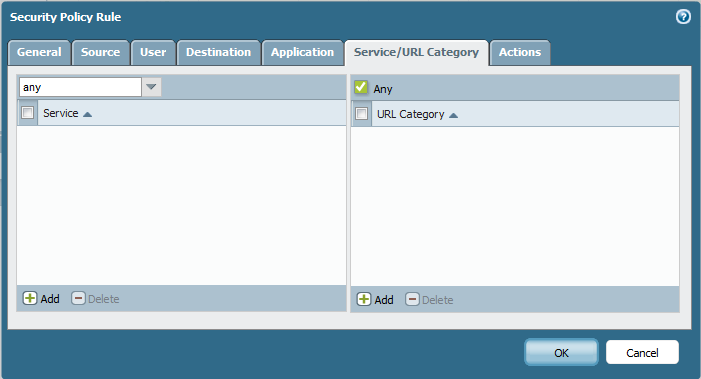
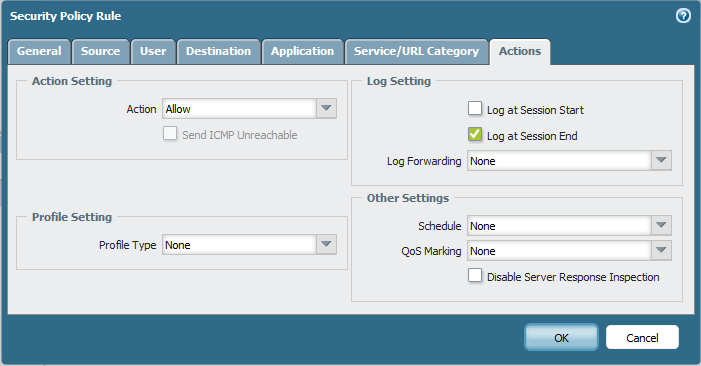
Last Part of Palo Alto is to Configure Security Policy Rule
Go to Policies – Security – Add new Choose a name and Rule type Universal also Interzone could work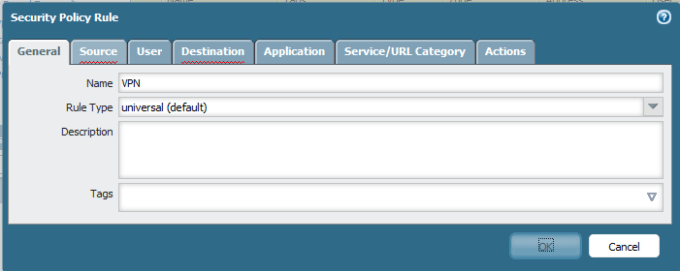
Choose Source as the Tunnel Interface Zone which was (VPN) Zone
Select my Destination As (LAN) so Ping from Site2 to me Work Perfectly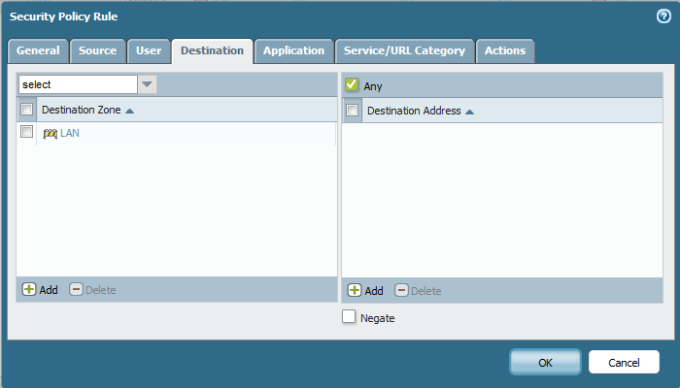
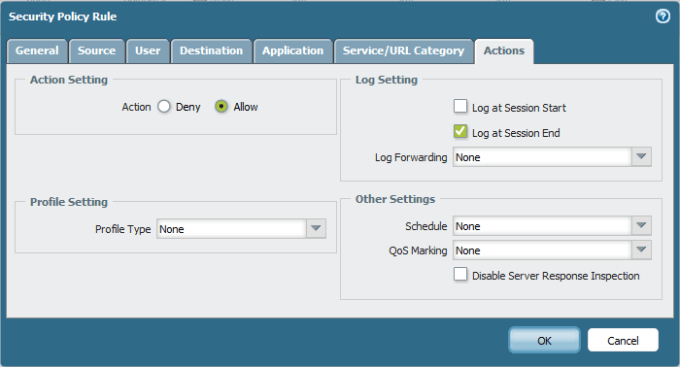
and Choose Action as Allow
Again do the Same to My Palo Alto user in Site1 to Allow their Ping to Reach Site2
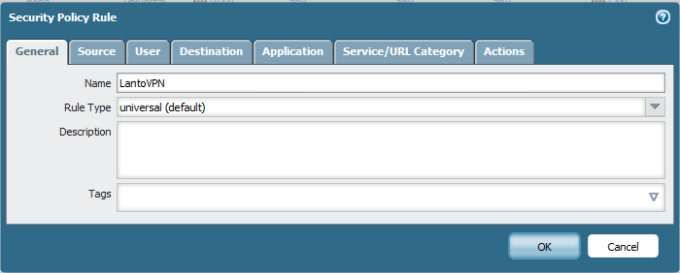
Source as LAN

Destination As VPN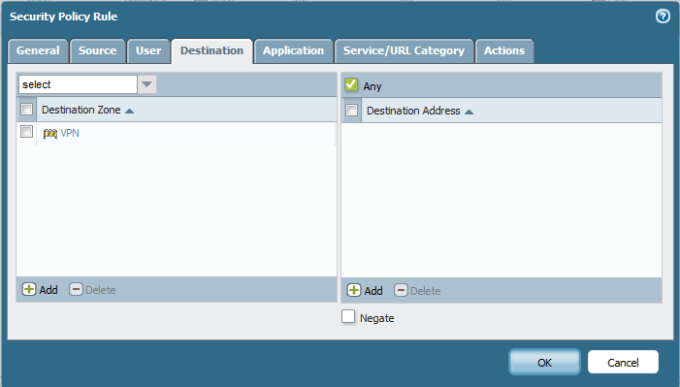
Now if you go to Network Tab – IPSec tunnel you will See the Status is (RED)
So Lets Start now in Cisco Side To Turn that light Off
First i Configure my Public Interface which Happen to be My FastEthernet 0/0 and My Loopback which my Internal Network

Next i Configure my IKE Phase 1 which Same Configuration to IKE1 in Palo Alto
Dont get scare if you show Run and you Don’t See group1 in the Configuration ;D
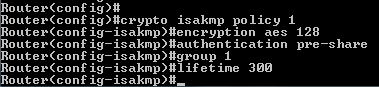
and Configure the Key Password and my Peer Address![]()
After that i Configure my IKE Phase 2
and Configure my IPSec Profile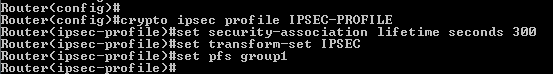
Then i Configure my Tunnel Interface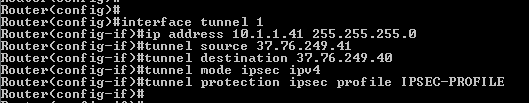
and Last but not Least i Configure my Route to Site 1 LAN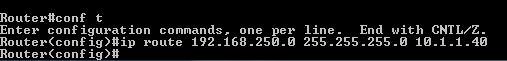
and now when i get back to my Palo Alto i see the Status turn Green
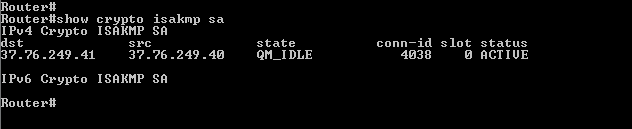
Also you can check the status on the Router
Now i ping from my Router to Palo Alto LAN Interface and it’s Work Perfectly
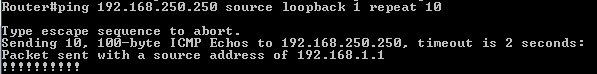
i Also Login by my PC and i Ping the loopback and ti work perfectly
;D






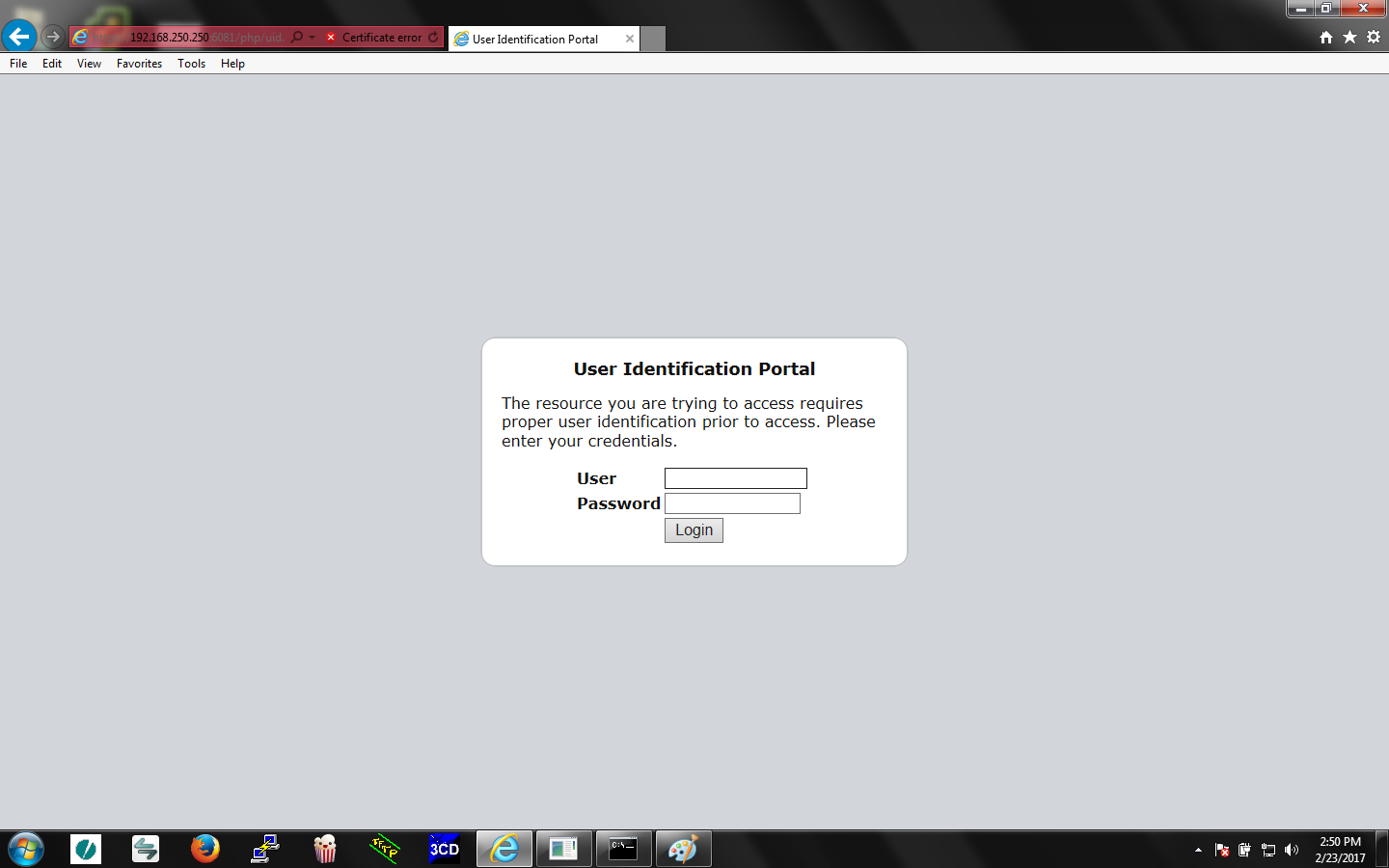
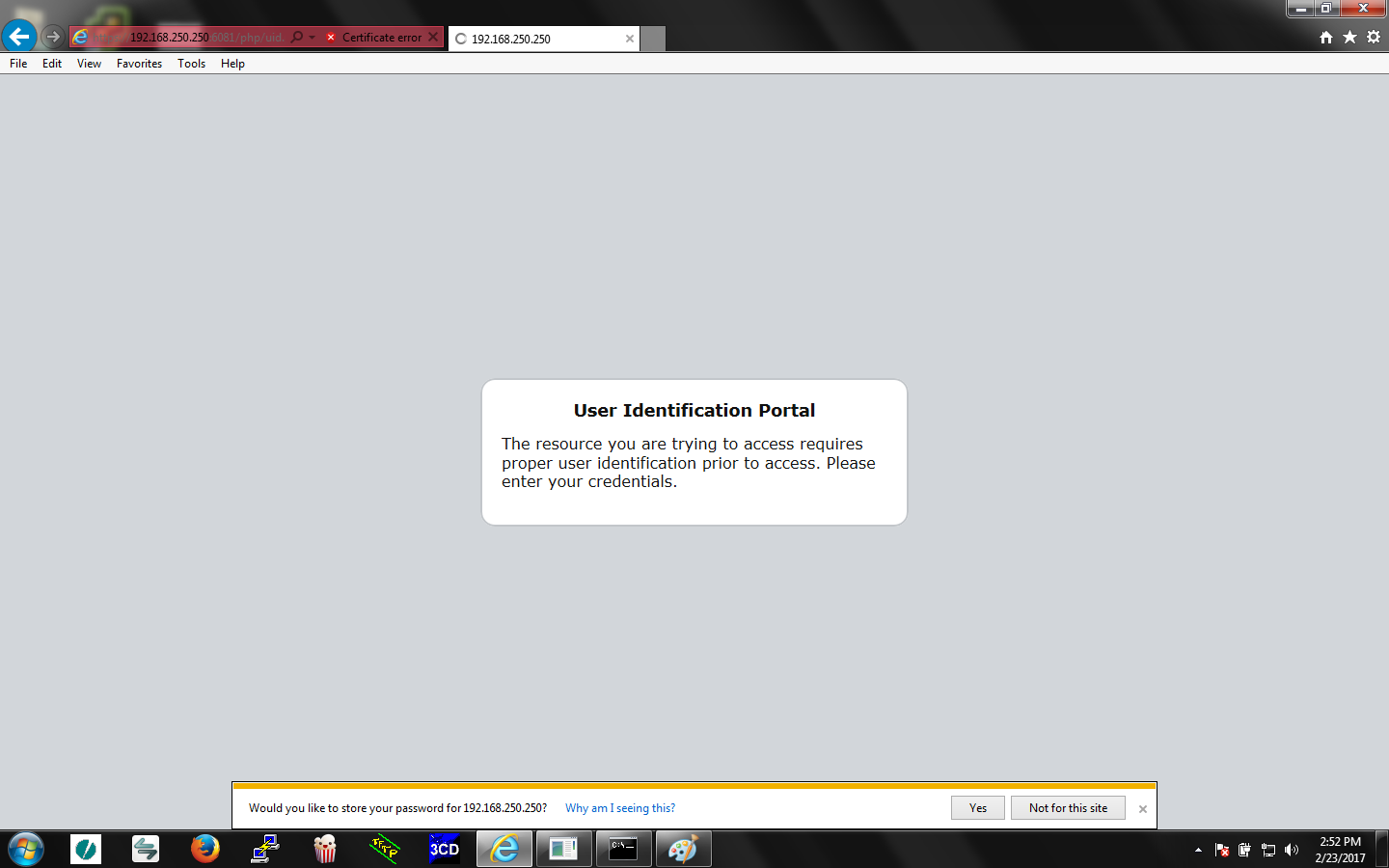






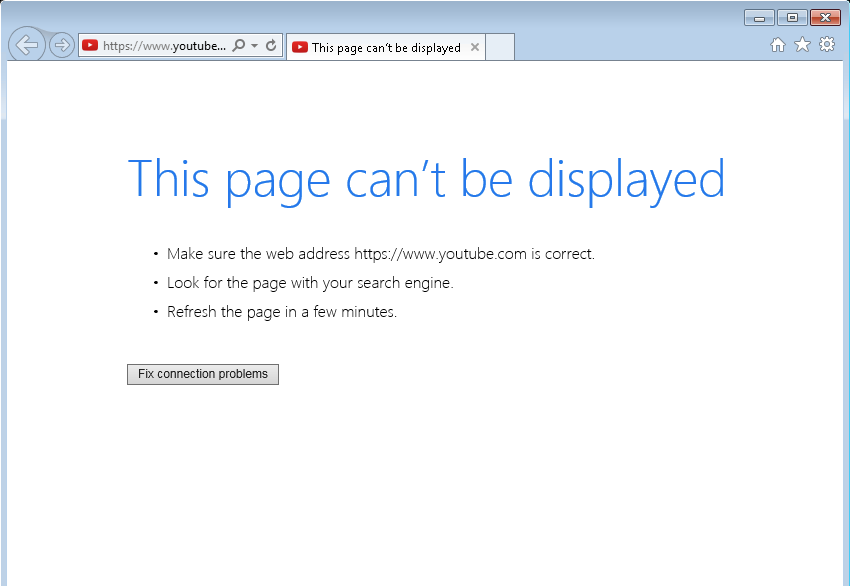




















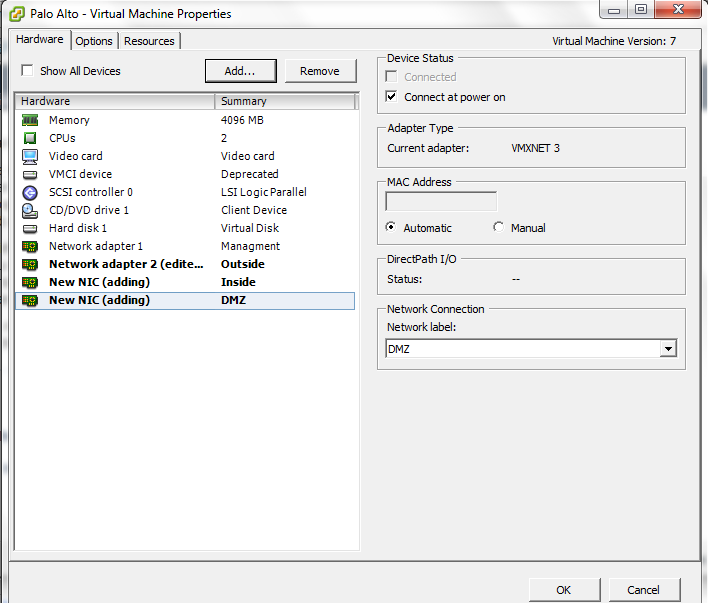
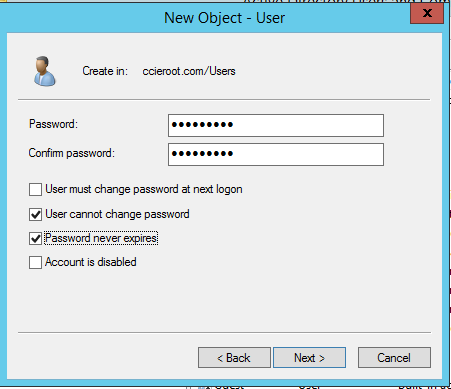
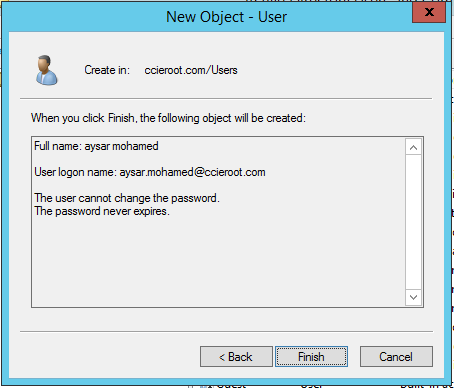
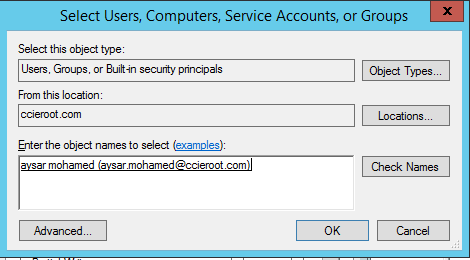
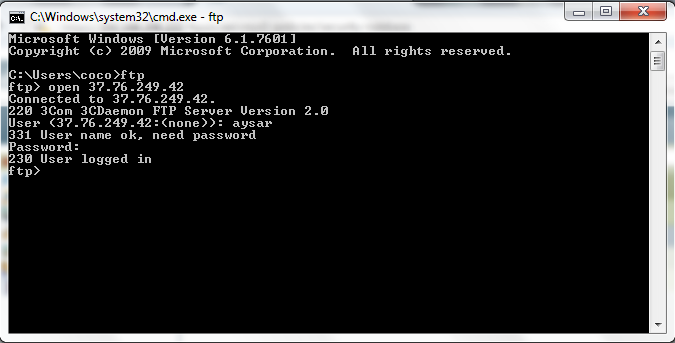
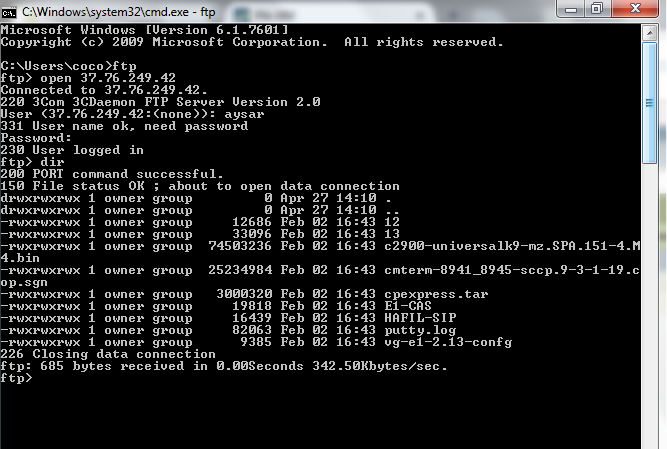
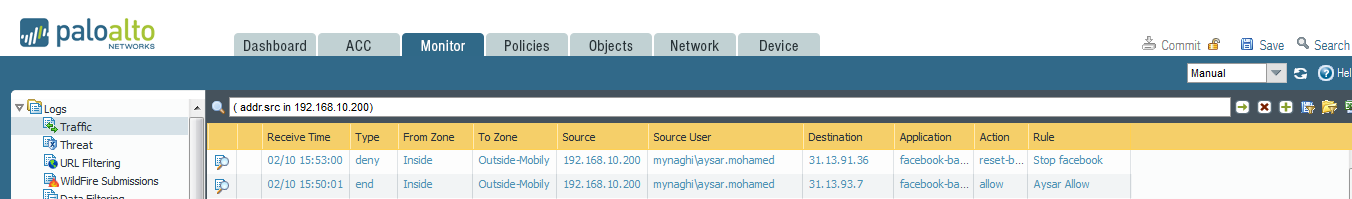 Now what if i want Aysar to view his Facebook but don’t want him to Chat with Anyone
Now what if i want Aysar to view his Facebook but don’t want him to Chat with Anyone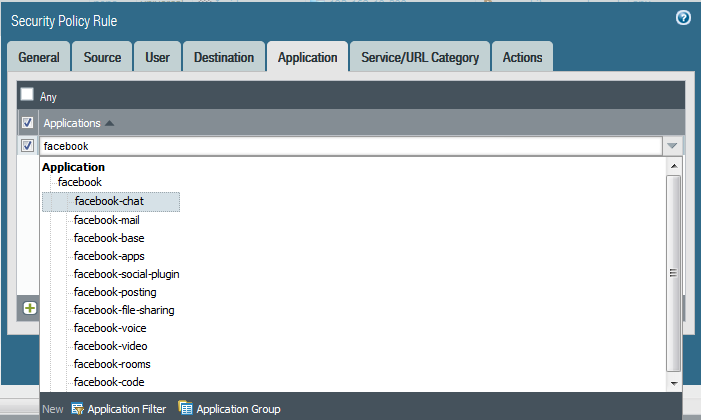





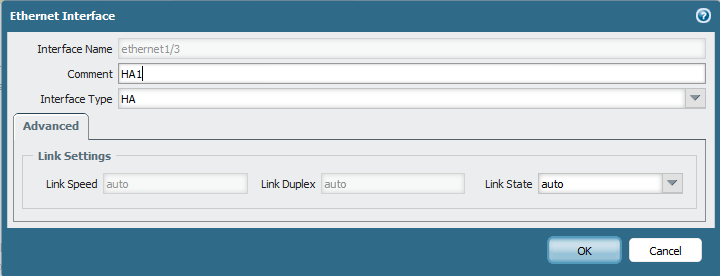























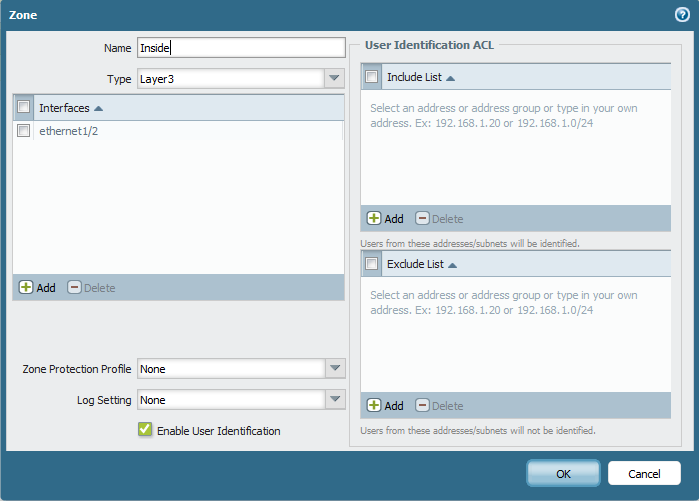










 Then Configure Ethernet 1/2 for DMZ gateway
Then Configure Ethernet 1/2 for DMZ gateway












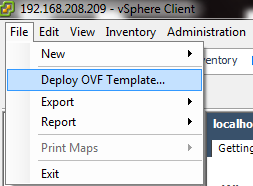






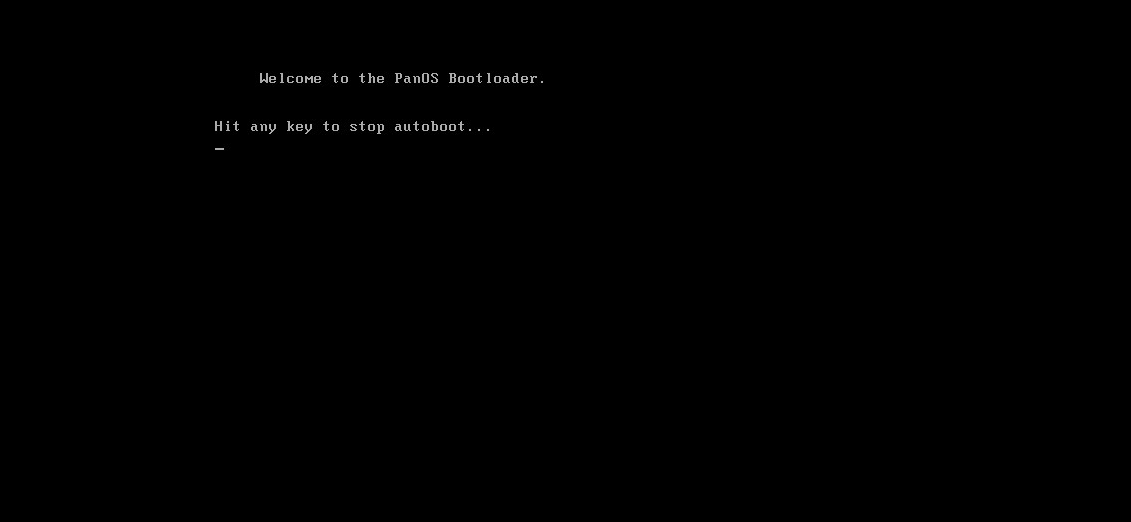
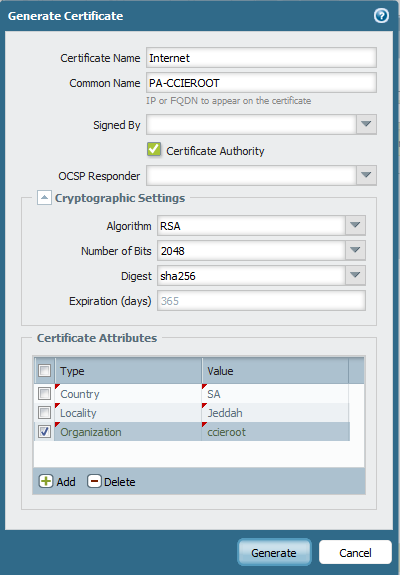
 Now we Finished with The Installation of the OVA
Now we Finished with The Installation of the OVA