The Most Important Element in CUCM World is the Media Resource. it’s used in order to allow an administrator to allocate media resources to particular devices.
There are five types of media resources available in Cisco:
Annunciator, Conference Bridges, Media Termination Point, Transcoder and Music On Hold
Annunciator is uses Cisco media streaming application service to play prerecorded announcements
Conference Bridges Without Saying it explain it self and can be either software or hardware applications
Media Termination Point or MTP can be used to transcode G.711 a-law audio packets to G.711 mu-law packets and vice versa. CUCM Software MTP can only work for G711 codec, however IOS MTP can have multiple codes
Transcoder when two Phones using different codecs would not be able to communicate so here were the Transcoder Job Come
Such Case Like conferencing, CUE use only G.711 so if another Coded used you need Transcoder, UCCX Support G.711 or G.729 so in case you need Both you need a Transcoder. Forward and transfer Call in case of Different Codec Also you need a Transcoder.
Music on Hold is the Boring Music that everyone hear when someone put us in hold ;D
So here i will guide you on how to configure my 4 Most Charming Feature (MTP, Transcoder, Conference and MOH)
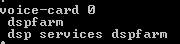
First We start by Configure the IOS Side
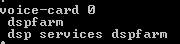
Allocating DSPs to a DSP Farm on Router
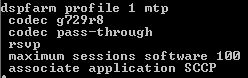
Then i Start to Configure the DSP-farm profiles for Each (MTP, Transcoder and Conference)
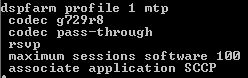

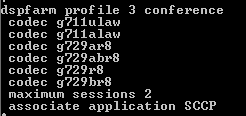
Note.Make Sure to Issue Command No Shut after Each Profile Configuration
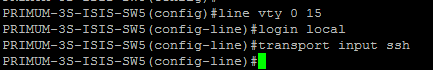
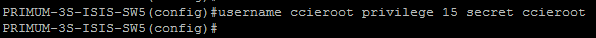
After the profiles are set up i start by the SCCP Configuration
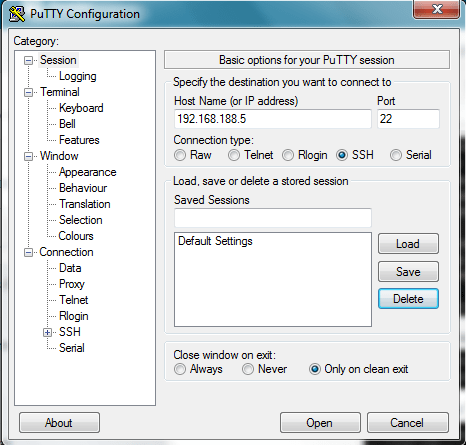
The routers use their Gigabit Ethernet 0/0 interface as the SCCP source interface, and the primary Cisco Unified Communication Manager should be 192.168.200.229 which my Publisher and for Better Practice it should be the Subscriber but i Only have one in the Lap

Last thing in IOS I Configure the SCCP Group
associated the CUCM with priority
associated Each Media Profile and Register with a name that i will use later in the CUCM Registration

Now the CUCM Part first start with MTP
go to Media Resource – Media Termination point – Add New
Select Cisco IOS Enhanced Software Media termination point
put the Name in the IOS which (MAINMTP)
Select the Device pool
Save – Reset

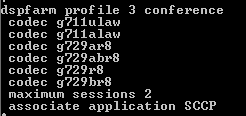
Now the Transcoder
go to Media Resource – Transcoder – Add New
Choose Cisco IOS Enhanced Media Termination point
Choose Device Name Configured in IOS Whcih (MAINXCODER)
Select the Device Pool
Save – Reset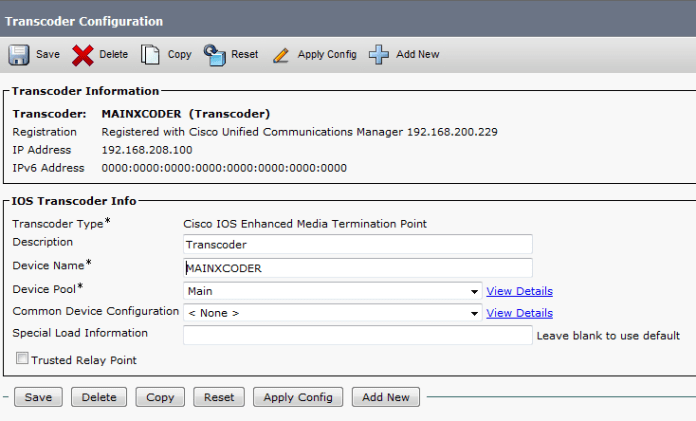
and Last the Conference
go to Media Resource – Conference Bridge – Add New
Choose Cisco IOS Enhanced Conference Bridge
Choose Device Name Configured in IOS Whcih (MAINCFB)
Select the Device Pool, Location and Device Security Mode as Non Secure
Save – Reset
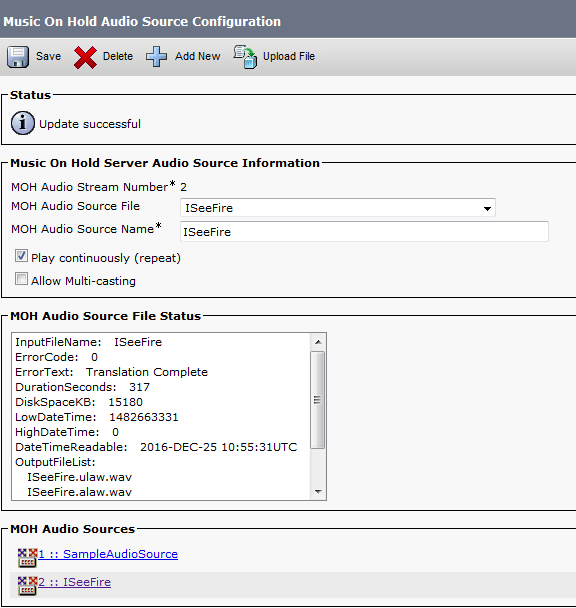
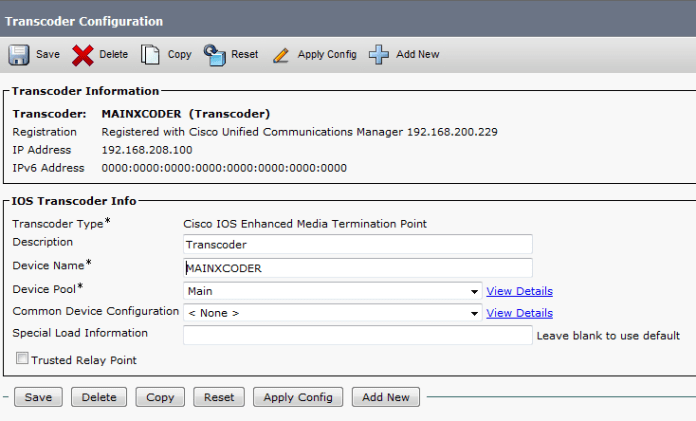
Last But Not Least to Configure MOH
Add the Audio File
Media Resources – MOH Audio File Management – Upload File From Desktop


 Then Create an MOH Source
Then Create an MOH Source
Go to Media Resources – Music On Hold Audio Sources – Add New
Choose Number and Select the Audio Source that you Just Upload
Last Thing is to Configure the MOH Server
Go to Media Resources – Music On Hold Server Audio Sources
Select the Device Pool, Location
Note.in Case of Multi Casting then you need to Check the Box for Enable Multi-cast Audio Sources on this MOH Server
Now Assign the MOH to the Phones
 Finally we Done with the Resources, it’s Time to add them all Under one group
Finally we Done with the Resources, it’s Time to add them all Under one group
go to Media Resource – Media Resource Group – Add New
Name it in my Case i Name it (MainOffice)
Choose the Resource you Just Configured (MAINMTP, MAINXCODER, MAINCFB and MOH_2 (MOH))
Add them
Save

Note.Also be Aware in case of Multi casting you need to Check the Box Use Multi-cast for MOH Audio (If at least one multi-cast MOH resource is available)
Now Create an Media Resource List and add the Group to it
go to Media Resource – Media Resource Group List – Add New
Name it in my Case i Name it (MainOffice)
Choose the Media Resource Group I Just Configured

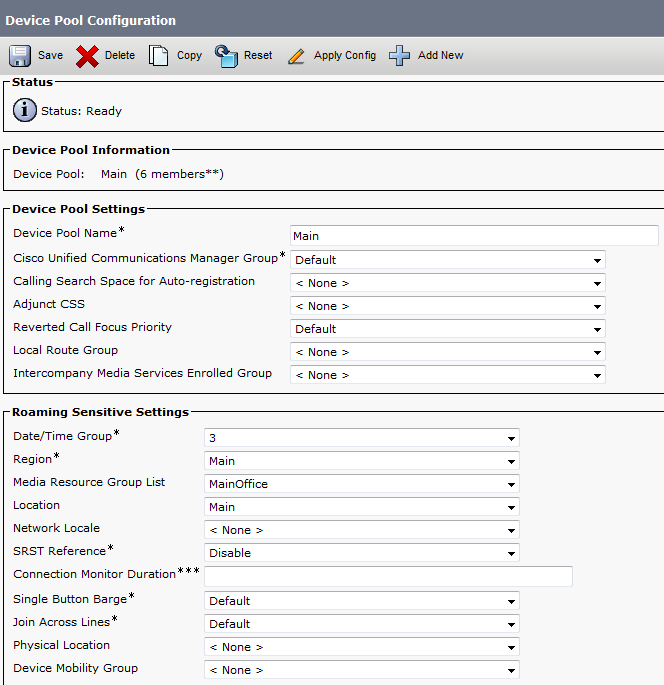
Finally Assign the Media Resource Group List to the Device pool 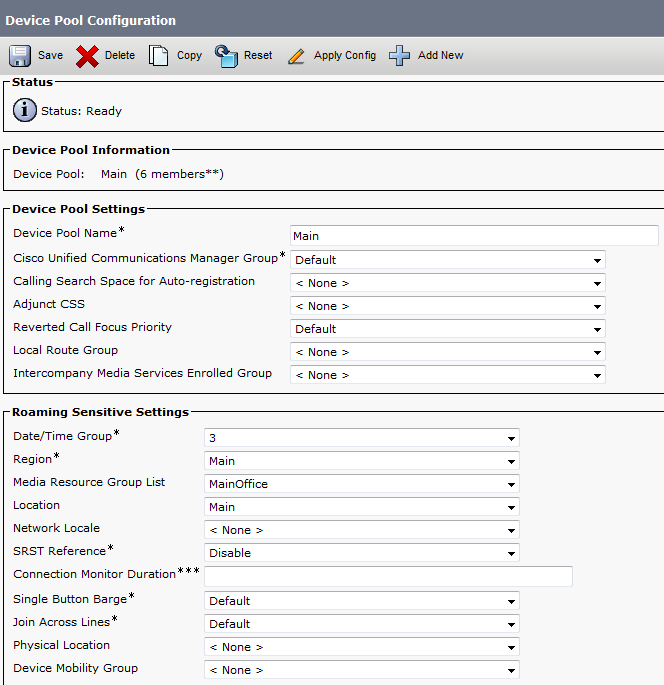
And Done
now you Allocated the Media Resource List i Configure for Each Member of this Device Pool
For Conference check this Link
For Music on Hold Video check this link














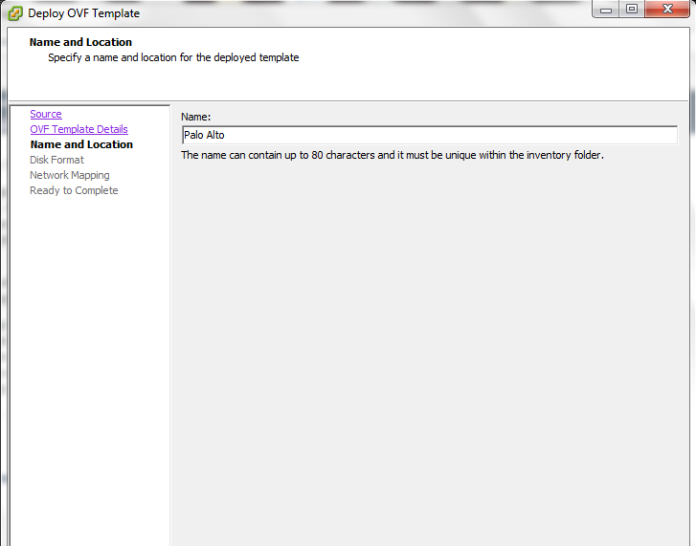



 Now we Finished with The Installation of the OVA
Now we Finished with The Installation of the OVA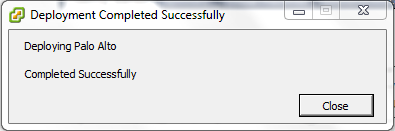








































 Then Create an MOH Source
Then Create an MOH Source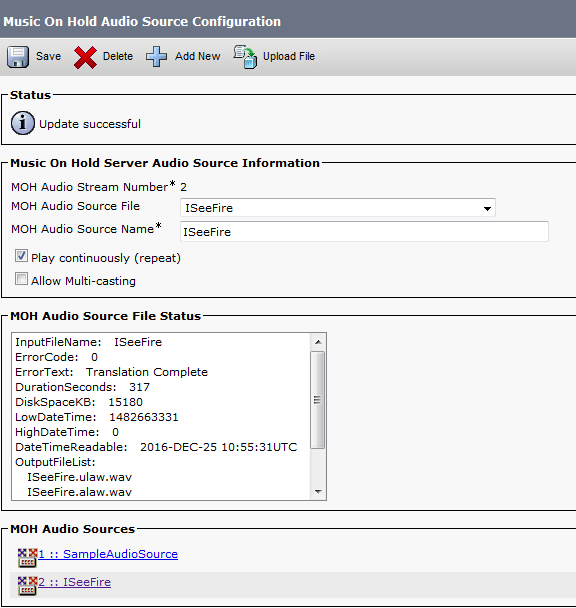

 Finally we Done with the Resources, it’s Time to add them all Under one group
Finally we Done with the Resources, it’s Time to add them all Under one group